Contents
How to Add SPF and DKIM to All Domains in cPanel Servers
Question: How can I add SPF and DKIM to all domains in cPanel server? Answer: You can do it with this tyny handy script that we will show you below using the command line from the root user of your cPanel server.
SPF and Domain Keys (DKIM) are one of the best practices you can do for your mail services, and for your users’ mail services to authenticate your email in the right way. These features provide information about incoming mail from your server. Email servers use this authenticated information to verify that a trusted sender sent the messages, and not a 3rd party illegitimate user.
SPF and DKIM records help to avoid spam issues, ISPs blocking your emails and a lot of more issues related to email authentication.
Add a SPF record and DKIM on cPanel for a particular domain
The best way to do it is from the cPanel control panel of each domain.
- Login to cPanel.
- Click on ‘Email Authentication’.
- Click ‘Enable’ button below DKIM and below SPF.
All done, now you have a generic DKIM and SPF record for your domain name.
Add SPF and DKIM for one particular domain from the command line
Using these simple commands you can generate SPF and DKIM records, just replace ‘username’ with your real cPanel username, and that’s all.
/usr/local/cpanel/bin/dkim_keys_install username /usr/local/cpanel/bin/spf_installer username
Add SPF and DKIM to All Domains on a cPanel Server
There is a simple way to add SPF and DKIM to all the domains inside your cPanel box. Just copy and paste this command and it will automatically add SPF records and DKIM records to all domains on the server.
cd /var/cpanel/users/ for user in * ; do /usr/local/cpanel/bin/dkim_keys_install $user && /usr/local/cpanel/bin/spf_installer $user ; done
As you see, this is a simple ‘for loop’ uses the same command we used before for both SPF and DKIM records, but the big difference is that this commands applies to all cpanel usernames inside the /var/cpanel/users/ directory.
That’s it, now you know how to Add SPF and DKIM to All Domains on your server. Do you know other ways to massive add SPF / DKIM records on cPanel servers?
Further reading:
How to clear DNS cache of your Operating System
DNS Cache (sometimes called DNS resolver cache) is the way your system has to grab a copy of the internet locations (IP addresses) of each website that you recently visited. DNS Resolver Cache is a DNS database that includes records of all the recent visits to websies and other internet domains.
The purpose of DNS Cache
This DNS Cache is stored in your operating system and serves as a fast way to know where the sites are located. However, if a website is migrated to a different network, using a different IP, and your DNS cache is still not updated, you will not be able to access the site unless you clear DNS cache on your OS.
Once you clear your DNS cache, your system will start retrieving the DNS Name Servers for the new DNS records of the website. This is basically how DNS Cache works. Now that you know the basics of DNS Cache, let’s learn how to clear DNS cache on different operating systems.
How to Clear DNS Cache on your local Operating System
Before getting into how to clear the DNS cache of your PC we will learn how to see what’s stored inside your local cache.
How can I see what’s inside my DNS Cache?
On Linux, the best way to see how your DNS Resolver cache is working, is to use dig command.
dig nixcp.com
Which will in return give you a DNS Record from your DNS Server specified in /etc/resolv.conf:
Expected output:
[webtech@localhost ~]$ dig nixcp.com ; <<>> DiG 9.10.4-P5-RedHat-9.10.4-4.P5.fc25 <<>> nixcp.com ;; global options: +cmd ;; Got answer: ;; ->>HEADER<nixcp.com. 1800 IN A 208.167.252.238
On Linux, you can find ways to clear the DNS cache and to resolve DNS records using dig, but not to see cached DNS records on your local system, at least I’m not aware of anything like that.
On Windows operating systems it is a different story. You can easily see the cached records by running these steps.
- Open the WinX Menu by pressing: Press Win+X.
- Right-click on “Command Prompt”
- Select “Run as Administrator”.
- Type “ipconfig /displaydns” and hit enter:
ipconfig /displaydns
You should get something like this as this:
C:\Documents and Settings\my.logon>ipconfig /displaydns Windows IP Configuration nixcp.com ---------------------------------------- Record Name . . . . . : nixcp.com Record Type . . . . . : 1 Time To Live . . . . : 1800 Data Length . . . . . : 4 Section . . . . . . . : Answer A (Host) Record . . . : 208.167.252.238 www.cpanel.com ---------------------------------------- Record Name . . . . . : www.cpanel.com Record Type . . . . . : 1 Time To Live . . . . : 100 Data Length . . . . . : 4 Section . . . . . . . : Answer A (Host) Record . . . : 208.74.123.68 redhat.com ---------------------------------------- Record Name . . . . . : www.redhat.com Record Type . . . . . : 1 Time To Live . . . . : 3600 Data Length . . . . . : 4 Section . . . . . . . : Answer A (Host) Record . . . : 209.132.183.105
Clear your DNS cache
The next methods will show you how to clear dns cache of your operating system. This will remove innacurate DNS caching information that will help you to avoid 404 errors while browsing recently migrated websites.
Windows 8
To clear your DNS cache on Windows 8 follow the next steps:
- Open the WinX Menu by pressing: Press Win+X.
- Right-click on “Command Prompt”.
- Select “Run as Administrator”.
- Run the following command:
ipconfig /flushdns
The output should show you this message if your dns cache was cleared successfully:
Windows IP configuration successfully flushed the DNS Resolver Cache.
Windows 7
In order to clear DNS cache on Windows 7, follow these steps:
- Click Start.
- Enter cmd in the Start menu search text box.
- Right-click on “Command Prompt”.
- Select “Run as Administrator”.
- Run the following command:
ipconfig /flushdns
The output should show you this message if your DNS cache was cleared successfully:
Windows IP configuration successfully flushed the DNS Resolver Cache.
Windows XP, 2000, and Windows Vista
Flush the DNS cache on Windows XP, 2000 or Vista is easy, follow these steps:
- Click Start.
- On the Start menu, click “Run”.
- If you don’t see the “Run” command in Vista: type “run” in the search bar.
- Run the following command inside the “Run” text box:
ipconfig /flushdns
The output should show you this message if your DNS cache was cleared successfully:
Successfully flushed the DNS Resolver Cache.
Linux Systems
Flush DNS cache on Linux is even easier than on Windows.
Follow the next steps to clear DNS cache on Linux if you are using a DNS Caching daemon:
- Open your terminal, log in as root.
- Restart the name service caching daemon:
Flush NSCD DNS cache
/etc/init.d/nscd restart
Flush bind DNS cache
/etc/init.d/named restart
or you can try
rndc restart
Flush dnsmasq DNS cache
service dnsmasq restart
MacOS® 10.10.4 and above
Clear your DNS Cache on macOS X 10.10.4 or above. Follow the next steps:
- Click Applications.
- Click Utilities.
- Click Terminal.
Type the following command:
sudo killall -HUP mDNSResponder
If the command succeeds the system will not show any output, this means the DNS cache was cleared successfully.
MacOS® 10.10.1, 10.10.2, 10.10.3
To clear your DNS cache if you use macOS X version 10.10 through 10.10.3, perform the following steps:
- Click Applications.
- Click Utilities.
- Click Terminal.
Run the following command:
sudo discoveryutil mdnsflushcache
If the command succeeds the system will not show any output, this means the dns cache was cleared successfully.
MacOS 10.7, 10.8, 10.9
Follow these steps to flush DNS cache on MacOS 10.7, 10.8, 10.9:
- Click Applications.
- Click Utilities.
- Double-click Terminal.
Type the following command:
sudo killall -HUP mDNSResponder
If the command succeeds the system will not show any output, this means the dns cache was cleared successfully.
MacOS 10.5 – 10.6
Follow this steps to flush the DNS cache on MacOS X 10.5 or 10.6:
- Click Applications.
- Click Utilities.
- Double-click Terminal.
- Type the following command:
sudo dscacheutil -flushcache
If the command succeeds the system will not show any output, this means the DNS cache was cleared successfully.
Clear the /etc/hosts file
On previous posts we’ve written about how to preview a website without switching DNS, on that post you saw that /etc/hosts can be configured to force a website to resolve on specific IP address.
If you are using the /etc/hosts file to force DNS lookups for a certain host, you may need to update your /etc/hosts file entries to avoid getting 404 errors.
Output example of /etc/hosts file with forced DNS records:
[webtech@localhost ~]$ cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 111.111.111.111 dev.nixcp.com 192.168.1.110 www.nixcp.com
As you see, there are two extra records (dev.nixcp.com and www.nixcp.com), if you are using that kind of records you may need to clear them out too.
How can I use hosts file to preview a website without switching DNS?
hosts file will always include one or two lines at the beginning, you must NOT modify those lines.
127.0.0.1 localhost
It can also look like this:
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
If you are a web developer or webmaster and you need to preview a website without switching DNS, you can include your domain name at the hosts’ file and map it to your server IP address. This will force your domain name to respond to your new server, without changing DNS at all.
Move to the end of the file, and add this line:
111.111.111.111 nixcp.com www.nixcp.com
Replace “111.111.111.111” with your real IP address, and “nixcp.com” with your real domain name.
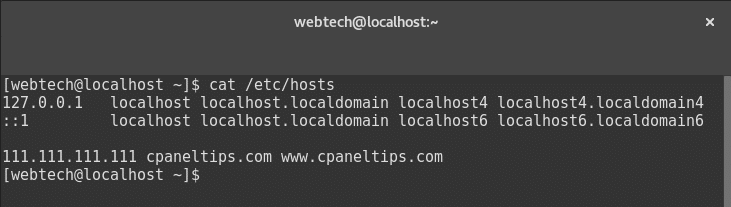
You can preview multiple domain names by adding more hosts to the line, example:
111.111.111.111 nixcp.com www.nixcp.com cpanel.com www.cpanel.com
Save the file, open your browser, clear your cache and finally type: www.yoursite.com
That’s all.
Now you are having a test preview a website without switching DNS name servers. It’s especially useful after server migrations when you need to pre-visualize your website content to make sure everything is working normally.
Once your tests are done, remove the line from the hosts’ file and change your DNS name servers.
How can I Configure Google MX records for on cPanel servers?
Google Apps Mail is one of the best email services out there. But it needs some manual configuration on your MX records in order to work properly. Today we will explore how to Configure Google MX records on cPanel servers.
How can I configure Google MX records on cPanel?
If one of your customers or you in the last case, needs to setup & configure Google MX records on cPanel servers, it can be done easily using the WHM interface.
Let’s move to:
WHM » DNS Functions » Edit DNS Zone
- Then search for the domain name where you need to set up the Google Apps MX records.
Click on Edit. - Delete all the existing MX records.
- Finally, add the following 5 records, one per line after this option: “Add New Entries Below this Line”.
Name/Host TTL Record Priority Value dominio.com. 3600 MX 1 ASPMX.L.GOOGLE.COM. dominio.com. 3600 MX 5 ALT1.ASPMX.L.GOOGLE.COM. dominio.com. 3600 MX 5 ALT2.ASPMX.L.GOOGLE.COM. dominio.com. 3600 MX 10 ALT3.ASPMX.L.GOOGLE.COM. dominio.com. 3600 MX 10 ALT4.ASPMX.L.GOOGLE.COM.
- You will see an option called “Email Routing for”, and make sure you select/activate this option: “Automatically Detect Configuration: Remote”.
- Press save and that’s all.
Important: ASPMX.L.GOOGLE.COM must be located at the top, as the first priority mail service. Do not move or alter the order of the MX records, or its priority.
Your MX records should look somehow like this:
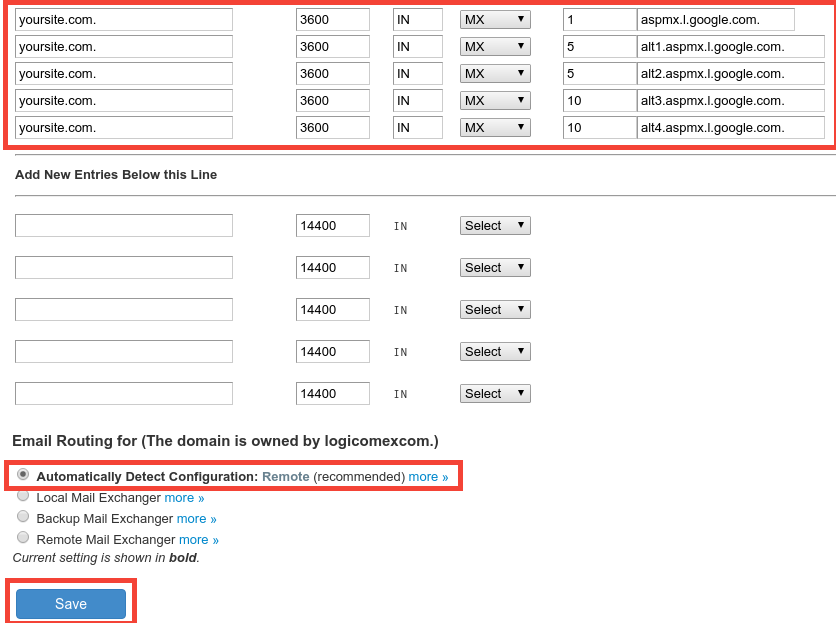
How can I verify Google MX records are working?
You can use Google Check MX tool to check if your Google MX records setup was done in the right way: https://toolbox.googleapps.com/apps/checkmx/
Now you know an easy way to configure Google MX records on cPanel servers. Your Google MX records should start propagating really fast, and be ready within 1 hour (almost all cases) to 48 hours max, in the worst case.
Remember that after this, you must create and manage all your email accounts from Google Apps Mail, and not from your cPanel server.
How can I configure Zoho MX records on cPanel?
Are there any good alternatives to Google Apps Mail? And the question is yes. There is Zoho. Today we will see how to configure Zoho MX records on cPanel servers.
Zoho Mail is a great alternative to Google Apps Mail. It includes a very good suite of online tools to help you to increase your productivity while keeping your service always online with their cloud-based services.
Setup Zoho MX Records by Updating your cPanel DNS Records
Zoho offers great email service, even with a free version of their services. Once you sing up for their service, you verify your account, create your domains and mail users. However, you won’t be able to receive an email if you don’t configure your MX records.
In this post, we will guide you to set up Zoho MX records on cPanel based servers, although this tutorial can also be useful for any other web hosting based platforms as Zoho uses the same MX records for all the setups.
How to setup / configure Zoho MX records on cPanel?
Zoho MX records can be set up using WHM panel:
WHM » DNS Functions » Edit DNS Zone
You should remove all existing MX records and set up three new MX records, as you see below:
[table “” not found /]The MX setup on WHM panel should look like this:
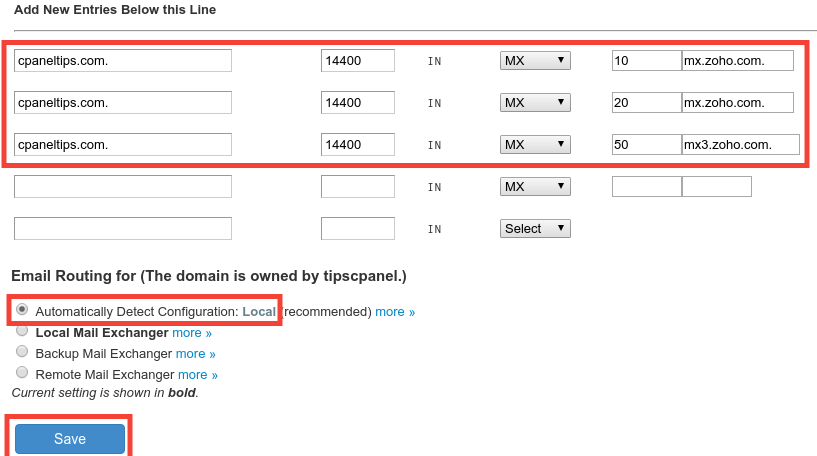
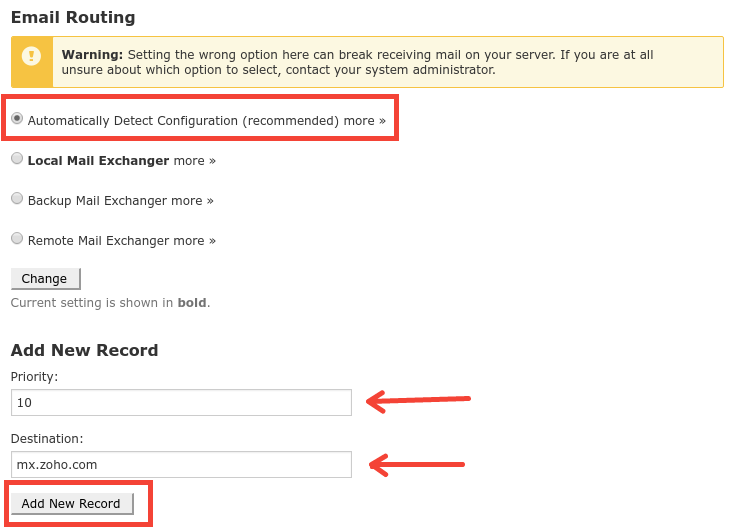
What if I don’t have access to WHM?
You still can setup your MX records from your cPanel control panel by following these steps:
- Login to your cPanel control panel using http://www.yoursite.com/cpanel
- Locate the option ‘MX Entries’ under the ‘Mail’ section.
- At Email Routing section, make sure to select Automatically Detect Configuration (recommended)
- At Add New Record, as stated before:
Priority: 10
Destination: mx.zoho.com
Then do the same for the other two records, click on ‘Add New Record’, this are the values for 2nd and 3rd MX entries:
Priority: 20
Destination: mx2.zoho.com
Priority: 50
Destination: mx3.zoho.com
That’s all.
See the output above:
Verify your Zoho MX setup is working as expected
You can verify your DNS zone using dig command from your local network, for example:
[[email protected] ~]$ dig MX yourdomain.com ; <<>> DiG 9.10.4-P4-RedHat-9.10.4-2.P4.fc25 <<>> MX zoho.com ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 25473 ;; flags: qr rd ra; QUERY: 1, ANSWER: 3, AUTHORITY: 6, ADDITIONAL: 8 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;zoho.com. IN MX ;; ANSWER SECTION: yourdomain.com. 300 IN MX 50 mx.zoho.com.
However, if you want to test against global locations, the best thing you can do is to use tools like DNS propagation.
At this time you should be all set, now you know how to configure Zoho MX records on cPanel easily and without any problems. As you see it takes only 5 minutes by editing your DNS zone and add a few MX records. The only thing you need to know it takes around 1 hour to 48 hs for full DNS propagation.
Further reading:
- Soho Mail Setup Docs: https://www.zoho.com/mail/help/adminconsole/cpanel.html#mx
How to rebuild Bind configuration on cPanel
Some times DNS servers on cPanel get corrupted, all the zones do not respond to queries, or the service simply doesn’t start at all after restarting the Linux service. That’s when you have to rebuild Bind configuration on cPanel to get all the dns queries working again.
How to Rebuild Bind configuration on cPanel
In order to fix this corruption on the DNS server we will first create a backup of the current DNS zones configuration, and then rebuild the DNS server using a cPanel tool called ‘rebuilddnsconfig’.
Create a backup of the current configuration
mv /etc/named.conf /etc/named.conf.bak -v
Rebuild your DNS server and zones
/scripts/rebuilddnsconfig
Restart the DNS server to apply changes:
/etc/init.d/named restart
All done, as you see, it’s easy to rebuild Bind configuration on cPanel and can be done within a few minutes. After this your DNS server should be working again, if not, check out if you have enough free disk space in your root and /tmp partitions. You may also open a cPanel ticket to get official support from cPanel tech team to investigate your issue.
Further reading:
How to find Bind version using Dig
By default BIND DNS server always reveals the version number. While this is not a security hole by itself, it’s the first point that a potential attacker will try to find out, the version number of your software and from that point he will try to find exploits for that version. That’s why today you will learn two important things: how to find bind version, and also how to protect against the same by hidding the version from any DNS queries.
How to check / find Bind version using Dig command
To know if you are vulnerable you can use a simple dig command against certain TXT records. For example:
dig chaos txt version.bind @ns1.nsname.com
The result will look like:
;; ANSWER SECTION: version.bind. 0 CH TXT "9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.3"
Where “@ns1.nsname.com” is the real name server that you are targeting.
How can I hide the BIND version?
Simple: edit your named.conf file (usually located at /etc/named.conf), and then add the ‘version’ directive under the options section. This will block the version.bind query against your name servers, example:
version "BIND";
This is how your code should look after the changes:
options
{
query-source port 53;
version "BIND";Once you are done, restart bind to apply the changes:
service named restart
At this point, you should know how to find bind version, and also how to hide it. If you need to read more about BIND, you can visit this Bind.
